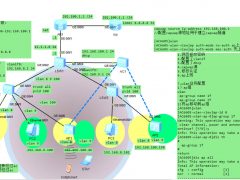
防火墙gre vpn隧道技术
FW1配置如下:
[FW1]dis cu
2025-06-14 12:49:50.410
!Software Version V500R005C10SPC300
#
sysname FW1
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
alias GE0/METH
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 11.1.1.1 255.255.255.0
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.1.1.1 255.255.255.0
#
interface Tunnel0
ip address 10.1.12.1 255.255.255.0
tunnel-protocol gre
source 11.1.1.1
destination 12.1.1.2
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
firewall zone dmz
set priority 50
add interface Tunnel0
#
ip route-static 0.0.0.0 0.0.0.0 11.1.1.254
ip route-static 10.1.2.0 255.255.255.0 Tunnel0
#
firewall detect ftp
#
security-policy
rule name gre
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
source-address 11.1.1.1 mask 255.255.255.255
source-address 12.1.1.2 mask 255.255.255.255
destination-address 11.1.1.1 mask 255.255.255.255
destination-address 12.1.1.2 mask 255.255.255.255
action permit
rule name yewu
source-zone dmz
source-zone trust
destination-zone dmz
destination-zone trust
source-address 10.1.1.0 mask 255.255.255.0
source-address 10.1.2.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 10.1.2.0 mask 255.255.255.0
action permit
rule name to-isp
source-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
action permit
#
nat-policy
rule name to-isp
source-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
action source-nat easy-ip
AR1配置如下:
[isp]dis cu
[V200R003C00]
#
sysname isp
#
firewall zone Local
priority 15
#
interface GigabitEthernet0/0/0
ip address 11.1.1.254 255.255.255.0
#
interface GigabitEthernet0/0/1
ip address 12.1.1.254 255.255.255.0
#
interface GigabitEthernet0/0/2
ip address 13.1.1.254 255.255.255.0
FW2配置如下:
[FW2]dis cu
2025-06-14 12:58:16.750
!Software Version V500R005C10SPC300
#
sysname FW2
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 192.168.0.1 255.255.255.0
alias GE0/METH
#
interface GigabitEthernet1/0/0
undo shutdown
ip address 12.1.1.2 255.255.255.0
#
interface GigabitEthernet1/0/1
undo shutdown
ip address 10.1.2.1 255.255.255.0
#
interface Tunnel0
ip address 10.1.12.2 255.255.255.0
tunnel-protocol gre
source 12.1.1.2
destination 11.1.1.1
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface GigabitEthernet0/0/0
add interface GigabitEthernet1/0/1
#
firewall zone untrust
set priority 5
add interface GigabitEthernet1/0/0
#
firewall zone dmz
set priority 50
add interface Tunnel0
#
ip route-static 0.0.0.0 0.0.0.0 12.1.1.254
ip route-static 10.1.1.0 255.255.255.0 Tunnel0
#
firewall detect ftp
#
security-policy
rule name gre
source-zone local
source-zone untrust
destination-zone local
destination-zone untrust
source-address 11.1.1.1 mask 255.255.255.255
source-address 12.1.1.2 mask 255.255.255.255
destination-address 11.1.1.1 mask 255.255.255.255
destination-address 12.1.1.2 mask 255.255.255.255
action permit
rule name yewu
source-zone dmz
source-zone trust
destination-zone dmz
destination-zone trust
source-address 10.1.1.0 mask 255.255.255.0
source-address 10.1.2.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 10.1.2.0 mask 255.255.255.0
action permit
rule name to-isp
source-zone trust
destination-zone untrust
source-address 10.1.2.0 mask 255.255.255.0
action permit
#
nat-policy
rule name to-isp
source-zone trust
destination-zone untrust
source-address 10.1.2.0 mask 255.255.255.0
action source-nat easy-ip
验证:
业务流量的放行
验证:
可上网nat地址转换成功。
总结:抓包分析gre的外层包和内层包,封装包头嵌套







 中型wlan部署有线和无线实验
中型wlan部署有线和无线实验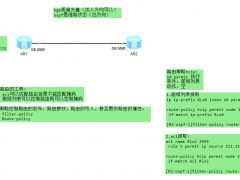 ospf的路由策略实验
ospf的路由策略实验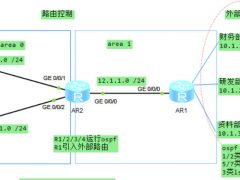 路由过滤与路由策略实验
路由过滤与路由策略实验 策略路由实验
策略路由实验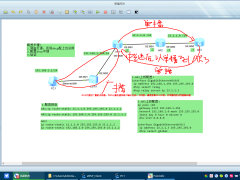 企业通过dhcp中继自动获取ip地址原理分析
企业通过dhcp中继自动获取ip地址原理分析 mpls部分php倒数第二跳抓包分析
mpls部分php倒数第二跳抓包分析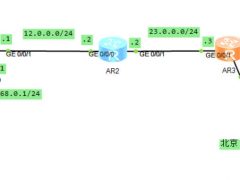 mpls vpn ldp动态lsp配置
mpls vpn ldp动态lsp配置 多协议标签交换 mpls vpn静态lsp配置
多协议标签交换 mpls vpn静态lsp配置